TECHNOLOGY
How Modern Commercial Security Systems Reduce Business Risks
In an increasingly complex operating environment, businesses face a wide range of risks that extend beyond traditional concerns, such as theft or vandalism. Unauthorized access, internal misconduct, data breaches, and operational disruptions can all threaten continuity and financial stability. Modern commercial security systems have evolved to address these challenges through integrated technologies that emphasize prevention, early detection, and informed response. Rather than functioning as isolated tools, today’s systems combine physical security, digital monitoring, and automated controls to create a more resilient risk management framework.
Advancements such as intelligent surveillance, access control systems, and real-time alerts allow organizations to identify vulnerabilities and respond more effectively to potential threats. These technologies also support better decision-making by generating data that can reveal patterns, inefficiencies, or emerging risks. For businesses seeking to understand how these systems are designed and implemented in real-world settings, general industry resources like signalsolutions.com provide insight into the components and principles behind modern security infrastructure. Overall, commercial security systems play a crucial role in mitigating uncertainty, facilitating compliance, and enabling organizations to maintain safe and reliable operations without relying solely on reactive measures.
AI-Driven Video Surveillance
Surveillance technology has undergone a transformation with the integration of artificial intelligence. Gone are the days of relying solely on human monitoring and analog cameras. AI-driven video surveillance provides real-time analysis, enabling the rapid identification of suspicious activities or policy violations without human oversight. These intelligent systems can detect and classify objects, recognize faces, and alert security teams to anomalies, minimizing incident response times and often preventing crimes before they escalate. AI-powered surveillance is becoming a cornerstone for proactive business risk management.
Cloud-Based Monitoring and Remote Access
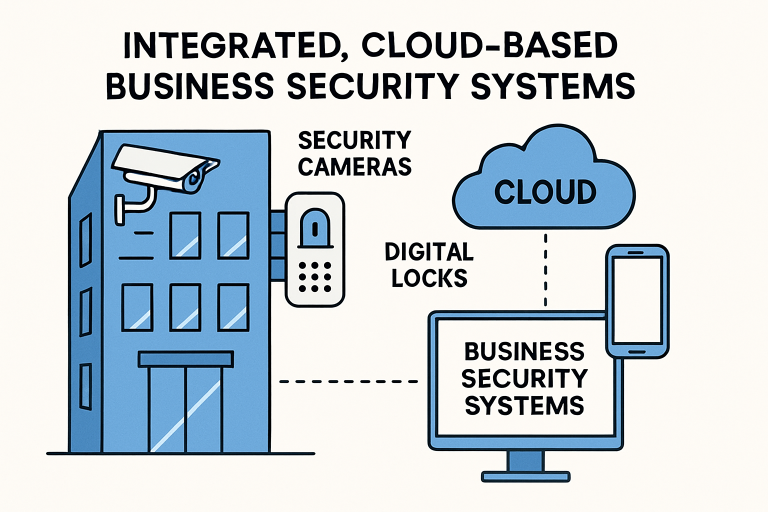
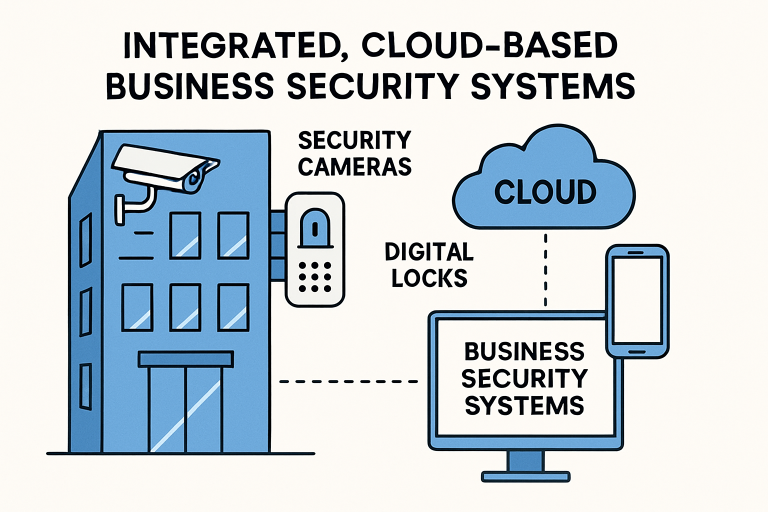
The adoption of cloud-based platforms has redefined how businesses monitor and control their security infrastructure. Cloud solutions allow for the centralized management of multiple locations, providing instantaneous access to live or recorded video feeds, access logs, and security events from any authorized device. This accessibility enables businesses to respond swiftly to emergencies, regardless of the location of their stakeholders.
Moreover, cloud-based systems can be scaled efficiently as a business grows, ensuring that new sites and users can be added with minimal disruption. Automated updates and cybersecurity features also provide protection against emerging digital threats, thereby reinforcing the overall security posture. This real-time, remote functionality proves invaluable for distributed teams and executives on the move.
 Advanced Access Control Systems
Advanced Access Control Systems
Modern access control extends far beyond traditional locks, utilizing technologies such as proximity cards, mobile credentials, and biometric authentication to enhance both security and convenience. These methods help prevent unauthorized entry and tailor access permissions to individual roles and schedules. For instance, cleaning staff may only have access to the building after hours, while IT personnel may have restricted access to server rooms.
Advanced access systems produce detailed audit logs, improving accountability and compliance—key considerations in regulated industries. Notably, smart access control can also integrate with other building systems, such as video surveillance and alarms, offering a unified response to threats and simplifying management for security personnel.
Integration of Physical and Cybersecurity
With the increasing convergence of digital and physical threats, integrating these security domains is vital. A physical breach often leads to cyber vulnerabilities, such as unauthorized access to servers or network devices. Accordingly, a unified approach that includes both on-premises and digital protections is essential for comprehensive risk mitigation.
Forward-thinking businesses develop strategies that monitor both access points and network events, closing potential gaps and strengthening incident response across the board. Industry authorities recommend implementing holistic policies and providing security training to all employees to ensure robust, integrated protection.
Mobile Access Control
Mobile devices are revolutionizing access control, eliminating the need for physical keys and cards. Employees and visitors receive unique digital credentials on their smartphones, which can be updated or revoked instantly if a device is lost or an individual’s role changes. This system significantly reduces the risks and administrative burdens associated with lost or duplicated keys.
Mobile access also enhances user experience, offering convenience and flexibility for businesses with remote work arrangements or multiple branches. With seamless integration into cloud-based monitoring, mobile control further streamlines facility management and emergency response protocols.
Data-Driven Security Planning
Gathering and analyzing security data is critical for identifying trends and making informed decisions about risk mitigation. By integrating data analytics and AI, security teams can predict incident hotspots, optimize resource allocation, and create actionable insights for ongoing protection. For example, analytics solutions can identify which entrances face the most traffic or which times are most prone to security incidents, enabling businesses to focus efforts where they’re needed most.
Data-driven strategies not only enhance prevention but also help justify investments by demonstrating measurable improvements in safety and efficiency. Companies that leverage analytics witness reductions in both security breaches and operational costs, supporting long-term business resilience.
Sustainable Security Solutions
Sustainability is becoming increasingly important in security deployments. Businesses are adopting solar, LED, and low-power technologies to minimize their environmental footprint and reduce costs. Battery-operated, wireless sensors and solar-powered cameras provide reliable performance with minimal energy consumption and no complex wiring, making them ideal for both new builds and retrofits.
By selecting eco-friendly security products and implementing green policies, businesses demonstrate commitment to environmental responsibility while simultaneously lowering utility expenses and maintenance needs. These choices align with broader corporate social responsibility initiatives and appeal to environmentally conscious stakeholders.
Conclusion
Modern commercial security systems are crucial for mitigating business risks and fostering a safe, resilient organizational culture. Embracing AI-driven surveillance, cloud-based management, advanced and mobile access control, and the convergence of physical and cyber protections provides companies with a layered, responsive defense against today’s threats. Combining data-driven planning with sustainable technologies further amplifies the benefits, enabling organizations to operate confidently and responsibly in a dynamic risk landscape. The businesses that keep pace with these security innovations will be best equipped to protect their people, property, and reputation well into the future.
TECHNOLOGY
Pxless: Revolutionizing Digital Design with Adaptive and Scalable Layouts

Introduction
In the world of digital design and development, the traditional approach to layout and structure has long relied on fixed pixel measurements. This method, which assigns specific dimensions to elements on the screen, ensures that the design looks consistent across devices. However, with the growing variety of screen sizes, resolutions, and devices used to access digital content, this method is beginning to show its limitations. Enter Pxless, a new concept in the realm of design and technology that seeks to address these challenges by focusing on scalability, flexibility, and adaptability.
While the term “Pxless” is still relatively new, it is gaining traction among designers, developers, and technologists who see it as a more efficient and future-proof approach to digital experiences. The central idea behind Pxless is to eliminate the reliance on fixed pixel measurements in favor of a more fluid, dynamic, and responsive system that enhances usability across devices and platforms. In this article, we will delve deeper into what Pxless is, how it works, and its potential impact on the world of digital design.
What Is Pxless?
Pxless is a design philosophy and approach that aims to move away from the traditional use of fixed pixel units in favor of more flexible, scalable, and adaptable systems. This means designing digital interfaces that can adjust to various screen sizes, resolutions, and devices without sacrificing usability or visual consistency.
The concept of Pxless is rooted in the idea that design should be fluid, not constrained by rigid measurements. Rather than defining elements in terms of specific pixel values, Pxless focuses on using relative units of measurement like percentages, ems, rems, and viewport units. These units are dynamic and scale based on factors like the size of the viewport or the device’s resolution. As a result, Pxless designs are more adaptable and can respond to different environments in a way that fixed-pixel designs cannot.
The Need for Pxless
The shift toward Pxless has been driven by the evolving landscape of digital technology. With the rise of smartphones, tablets, wearables, and other devices, there is a growing need for designs that can seamlessly adjust to various screen sizes and resolutions. The traditional approach of designing with fixed pixels was developed in a time when desktop computers and monitors were the primary devices for accessing the web. However, as new devices emerged, the limitations of fixed-pixel layouts became evident.
Fixed-pixel designs were often rigid, leading to issues like poor scaling, inconsistent layouts, and a lack of responsiveness across devices. For example, a website or app designed with a fixed-width layout might look perfect on a desktop monitor but appear awkward and difficult to use on a mobile phone or tablet. In contrast, Pxless design principles emphasize fluidity and adaptability, allowing digital experiences to work seamlessly across all screen sizes and resolutions.
Key Principles of Pxless Design
Fluid Layouts: One of the core principles of Pxless is the use of fluid layouts that adjust to the size of the screen. Rather than defining specific pixel widths and heights, Pxless layouts use relative units of measurement, such as percentages or viewport units. This ensures that elements on the page scale proportionally based on the available space, providing a more flexible and adaptable design.
Responsive Design: Pxless encourages the use of responsive design techniques, which allow digital experiences to adapt to different devices and screen sizes. This means that the layout, typography, and other design elements adjust dynamically based on the user’s device. By eliminating the reliance on fixed pixels, Pxless makes it easier to create designs that work well on desktops, smartphones, tablets, and other devices.
Scalable Units: Instead of using pixels as a fixed unit of measurement, Pxless promotes the use of scalable units like ems, rems, and percentages. These units are relative and adjust based on factors like the font size, viewport size, and device resolution. This makes it easier to create designs that are not only more flexible but also more accessible, as users can adjust the size of elements to suit their preferences.
Consistency Across Devices: One of the primary benefits of Pxless is its ability to create consistent user experiences across different devices. Since the design is based on relative units that scale dynamically, users can enjoy a similar experience whether they are using a desktop computer, smartphone, or tablet. This eliminates the need for multiple versions of a website or app, streamlining the design and development process.
Efficiency and Performance: Pxless is not just about flexibility and adaptability; it is also about improving the efficiency of the design and development process. By using scalable units and flexible layouts, designers can create more efficient code that reduces the need for excessive media queries, fixed pixel values, and other time-consuming adjustments. This can lead to faster load times, improved performance, and a more streamlined workflow.
How Pxless Benefits Different Digital Platforms
Web Design
In the realm of web design, Pxless offers a more modern and adaptable approach to creating layouts that work well across a variety of screen sizes. Traditional web design often relied on fixed-width designs or used CSS media queries to adjust layouts for different screen sizes. While media queries are still important, the use of Pxless principles ensures that designs are inherently flexible, reducing the need for excessive adjustments for different devices.
With Pxless, web designers can create fluid layouts that adjust based on the viewport size, meaning that users will have a consistent experience whether they are browsing on a large desktop monitor or a small smartphone screen. This approach also improves accessibility, as text and interface elements can be scaled dynamically to accommodate different users’ preferences.
Mobile Development
In mobile app development, Pxless provides an opportunity to create more responsive and user-friendly interfaces. Since mobile devices come in various sizes and resolutions, developers often face the challenge of creating apps that look great and function well on all devices. By adopting Pxless principles, mobile app developers can design interfaces that scale smoothly across different screen sizes, eliminating the need for multiple design versions.
Pxless also enhances the performance of mobile apps by reducing the reliance on fixed pixel values, which can lead to inefficient and bulky code. Instead, developers can use scalable units to create lightweight, optimized interfaces that provide a better user experience.
Digital Products and Software
Beyond websites and mobile apps, Pxless can also be applied to other digital products and software applications. From desktop applications to wearables and IoT devices, Pxless enables designers and developers to create user interfaces that are adaptable to a wide range of screen sizes and resolutions.
As more devices enter the market, from smartwatches to augmented reality glasses, the need for scalable and adaptable interfaces becomes even more crucial. Pxless provides a way for developers to create experiences that work seamlessly across these diverse platforms without requiring constant adjustments or redesigns.
The Impact of Pxless on User Experience
At its core, Pxless is about improving the user experience. By embracing flexibility and adaptability, Pxless ensures that users can interact with digital products in a way that is intuitive and efficient, regardless of the device they are using. The elimination of fixed pixel measurements means that elements on the screen adjust to the user’s needs, providing a consistent experience that is easy to navigate.
For instance, with Pxless design, text and images can scale proportionally, making it easier for users to read and interact with content. Buttons and interface elements can adjust in size, ensuring they are touch-friendly on smaller screens while remaining appropriately sized for larger displays. This leads to a more inclusive and accessible digital experience for all users, regardless of the device they use.
The Challenges of Implementing Pxless
While Pxless offers many benefits, it is not without its challenges. The transition from fixed-pixel design to a more fluid and scalable approach requires a shift in mindset for many designers and developers. For teams accustomed to working with fixed measurements, adopting Pxless principles may involve a learning curve and a rethinking of how layouts are structured.
Moreover, implementing Pxless in an existing design or product can be complex, especially for legacy systems that rely on fixed pixel values. However, as the demand for responsive and adaptable designs grows, the adoption of Pxless is likely to become more widespread, with tools and frameworks evolving to support this approach.
Conclusion
Pxless represents a significant step forward in the evolution of digital design and development. By moving away from the limitations of fixed pixel measurements, Pxless provides a more flexible, scalable, and efficient way to create digital experiences that work seamlessly across devices. Whether in web design, mobile development, or broader digital products, Pxless offers a modern solution to the challenges posed by an increasingly diverse and complex digital landscape.
As more designers and developers embrace the principles of Pxless, we can expect to see a shift toward more adaptable, user-friendly interfaces that prioritize efficiency and usability. While it may still be a relatively new concept, Pxless has the potential to shape the future of digital design and development, offering a more inclusive and scalable approach to creating experiences that work for everyone, everywhere
FAQ’s
1. What is Pxless design?
Pxless is a design approach that eliminates fixed pixel measurements, using fluid and scalable systems to create adaptive digital experiences.
2. How does Pxless improve usability across devices?
Pxless ensures that layouts adapt fluidly to various screen sizes and resolutions, enhancing usability and providing a consistent experience.
3. What are the main benefits of using Pxless?
It offers flexibility, scalability, responsiveness, and efficiency, making digital designs more adaptable and improving performance across devices.
4. Is Pxless applicable only to web design?
No, Pxless is applicable to web design, mobile apps, and any digital product that needs to adapt to multiple screen sizes.
5. What challenges come with adopting Pxless?
Adopting Pxless may require a shift in design mindset and adjustments in existing systems, but it improves long-term usability and performance.
TECHNOLOGY
How SD-WAN Solutions Drive Network Agility for Global Businesses

Introduction
Modern global businesses rely on agile, resilient network infrastructure to power their operations, connect remote offices, and deliver seamless experiences to users worldwide. As digital transformation accelerates and organizations demand higher speed, reliability, and security, traditional wide area networking approaches have struggled to keep up. This shift has led to the adoption of Software-Defined Wide Area Networking (SD-WAN), a solution transforming how enterprises approach connectivity. Today, SD-WAN providers play a critical role in helping businesses adapt to evolving demands.
SD-WAN platforms offer businesses an intelligent, automated way to manage their wide-area networks while ensuring high application performance and data protection. This article explores how SD-WAN solutions offer powerful advantages for globally distributed organizations and why the technology is capturing the attention of IT leaders across different industries.
Understanding SD-WAN
SD-WAN represents a significant shift in network architecture. Rather than relying on a single type of connectivity or static routing, SD-WAN enables organizations to leverage multiple connection types, such as MPLS, broadband, LTE, and fiber, for their wide-area networks. Using a virtualized overlay, SD-WAN centrally manages these connections, steering traffic dynamically based on real-time conditions. By abstracting network management into software, businesses gain a unified platform for deploying, monitoring, and securing their WAN with far greater agility and efficiency than before.
Unlike traditional WANs, which can be complex and inflexible, SD-WAN reduces operational complexity through centralized, policy-based control. Network administrators can remotely configure, optimize, and troubleshoot network performance, drastically reducing the time and resources required for changes or troubleshooting across distributed office locations. This centralized management is a foundational benefit for organizations with global reach.
For a closer look at the technology’s principles and market developments, consult this Tech Republic explainer on SD-WAN.
Benefits of SD-WAN for Global Businesses
Enterprises with dispersed workforces, remote offices, and growing connectivity needs find numerous advantages in SD-WAN solutions:
- Enhanced Performance: SD-WAN continuously analyzes network traffic and automatically selects the optimal path based on application needs and current network health. This dynamic routing minimizes latency, reduces packet loss, and improves the end-user experience, particularly for cloud-based applications.
- Improved Security: Built-in encryption, firewalls, and secure segmentation capabilities ensure sensitive information travels securely across public and private networks, addressing growing cybersecurity concerns for distributed businesses.
- Cost Efficiency: By combining affordable public internet circuits with legacy MPLS links, organizations can reduce dependence on costly single-provider solutions and achieve significant networking cost savings.
- Scalability: Provisioning new sites or adjusting network capacity can be accomplished quickly and remotely, expediting business expansion without large capital investment or extended deployment timelines.
By combining these benefits, SD-WAN fuels operational agility, enabling companies to remain competitive even as their global footprint expands. According to a recent Gartner report, modern network and security architectures such as SD-WAN are increasingly essential for supporting digital transformation initiatives across sectors.
Key Drivers of SD-WAN Adoption
Several core trends are propelling the rapid adoption of SD-WAN among global enterprises:
- Cloud Migration: With more mission-critical applications moving to cloud platforms, organizations must ensure fast, reliable connectivity between users and apps, regardless of location. SD-WAN is uniquely positioned to optimize cloud access and performance.
- Security Concerns: The growing sophistication of cyber threats and the expansion of the remote workforce have made robust security non-negotiable. SD-WAN’s integrated firewall, VPN, and advanced threat protection features proactively address these risks.
- Operational Efficiency: The centralized, software-driven approach to WAN management reduces complexity, improves visibility, and automates many administrative tasks, freeing up IT teams to focus on strategic goals rather than routine maintenance.
Managed SD-WAN Services
For many organizations, the expertise required to deploy and manage an SD-WAN solution in-house can be a barrier. That is why an increasing number of businesses are opting for managed SD-WAN services, entrusting the design, implementation, and day-to-day management of their network to specialized experts. Managed solutions deliver these key benefits:
- Expertise: Providers bring deep experience and best practices, reducing risk and ensuring an optimized deployment that aligns with business objectives.
- Cost Savings: Migrating to a managed model lowers both capital and operational spending on network infrastructure and personnel.
- Focus on Core Business: By handling network management, providers enable internal IT teams to redirect their efforts toward innovation and business growth rather than network troubleshooting.
Case Studies
Real-world use cases showcase the measurable impact of SD-WAN deployments in global businesses:
- Nestlé’s Network Transformation: Nestlé leveraged Cisco SD-WAN to revamp its global network, spanning 1,700 locations across 185 countries. This overhaul delivered greater resiliency, agility, and operational efficiency. The revamped network architecture allowed for streamlined application management, robust security, and higher uptime.
- Egypt’s Enhanced Business Agility: Egypt used Cisco SD-WAN technology to power its managed services offering for local businesses. The solution enhanced network security, improved performance, and simplified network management for business clients across Egypt.
Future Trends in SD-WAN
The SD-WAN market is poised for sustained, robust growth. Research indicates a projected compound annual growth rate (CAGR) exceeding 30 percent through 2034, as organizations increasingly rely on advanced automation, analytics, and artificial intelligence within networking environments. SD-WAN architectures will continue to evolve, offering even more automation, embedded threat intelligence, and seamless integration with cloud-native security services. Businesses that embrace the latest trends in SD-WAN will enjoy resilient, high-performance networks equipped to handle the complexities of global operations. For additional insights into market trajectories, consult this IDC analysis.
Conclusion
SD-WAN solutions are changing how global businesses approach connectivity, performance, and security. By leveraging centralized control, dynamic traffic management, and reduced networking costs, companies can navigate the challenges of digital transformation with confidence. As the adoption of SD-WAN accelerates, businesses are better positioned to achieve network agility, operational efficiency, and a competitive edge on the global stage.
TECHNOLOGY
w0wkino: Best Practices for Secure Online Movie Streaming
In the early days of the internet, digital platforms were judged mostly by whether they worked. Speed, stability, and basic usability were enough. But as technology matured and audiences became more discerning, something else began to matter just as much: how a product felt to use. This is where w0wkino quietly enters the conversation—not as a buzzword or a fleeting trend, but as a philosophy that reflects how modern digital experiences are evolving.
w0wkino represents a shift in thinking. It sits at the intersection of technology, human behavior, and creative intent, offering a framework for building digital environments that are not only functional but emotionally intelligent. For entrepreneurs, tech readers, and founders, understanding w0wkino is less about mastering a tool and more about recognizing a mindset that is shaping the next generation of platforms.
Understanding the Core Idea Behind w0wkino
At its core, w0wkino is about intentional design in digital systems. It emphasizes coherence—between interface and purpose, between user expectations and system responses. Rather than focusing on isolated features, w0wkino encourages creators to view products as living ecosystems where every element supports the whole.
This idea resonates strongly in today’s market because users no longer tolerate friction. A platform might be powerful, but if it feels confusing or emotionally cold, adoption suffers. w0wkino addresses this by aligning structure, interaction, and narrative. The result is a digital experience that feels intuitive without being simplistic and sophisticated without being overwhelming.
Importantly, w0wkino is not tied to a single industry. Its principles apply equally to SaaS platforms, content ecosystems, community-driven products, and emerging AI-powered tools. Wherever humans interact with technology, the w0wkino mindset can be applied.
Why w0wkino Matters in a Saturated Digital World
The modern digital landscape is crowded. New platforms launch daily, each promising innovation, speed, or disruption. Yet very few leave a lasting impression. w0wkino matters because it shifts the competitive advantage away from raw functionality and toward meaningful experience.
Users today make decisions quickly. They sense quality almost instantly, often before they can articulate why something feels right or wrong. w0wkino acknowledges this reality by prioritizing clarity, emotional flow, and consistency. When done well, it reduces cognitive load and builds trust subconsciously.
For founders, this has direct business implications. Products built with a w0wkino-oriented approach often see stronger engagement, longer retention, and more organic advocacy. People don’t just use them; they remember them. In an economy driven by attention, that distinction is powerful.
The Strategic Role of w0wkino for Entrepreneurs
Entrepreneurs often face pressure to ship fast, iterate constantly, and respond to market signals. While speed is important, w0wkino reminds builders that direction matters just as much as momentum. Without a coherent experience strategy, rapid growth can amplify flaws rather than strengths.
By integrating w0wkino early, entrepreneurs gain a strategic lens. Decisions about features, branding, and user journeys are filtered through a single guiding principle: does this enhance the overall experience? This reduces internal friction and helps teams align around a shared vision.
w0wkino also supports scalability. When a product grows, complexity naturally increases. A strong experiential framework ensures that expansion feels intentional rather than chaotic, preserving usability even as functionality deepens.
How w0wkino Influences Product Design and Technology
From a design perspective, w0wkino encourages balance. Interfaces are clean but expressive. Interactions feel responsive without being distracting. Visual elements support comprehension instead of competing for attention. The goal is not minimalism for its own sake, but purposeful restraint.
On the technical side, values architecture that supports adaptability. Systems are built to evolve alongside users rather than forcing users to adapt to rigid structures. This often means modular development, thoughtful data flows, and flexible front-end logic.
The following table highlights how traditional digital thinking compares with a w0wkino-inspired approach:
| Aspect | Traditional Digital Approach | w0wkino-Oriented Approach |
|---|---|---|
| Design Focus | Visual appeal or trends | Experience coherence |
| Feature Strategy | Additive and reactive | Intentional and narrative-driven |
| User Journey | Linear and task-based | Contextual and adaptive |
| Scalability | Technical first | Experience-first growth |
| Long-Term Impact | Functional reliability | Emotional and functional resonance |
This contrast explains why is gaining attention among builders who think beyond short-term metrics.
w0wkino and the Human Side of Technology
One of the most compelling aspects of is its respect for human behavior. Technology does not exist in a vacuum; it operates within cultural, emotional, and psychological contexts. w0wkino acknowledges this by treating users as participants rather than endpoints.
This perspective is especially relevant in an era of automation and AI. As systems become more powerful, the risk of alienation increases. w0wino acts as a counterbalance, ensuring that efficiency does not come at the cost of empathy.
By designing with emotional intelligence, platforms can support focus, reduce stress, and foster a sense of control. These qualities may seem intangible, but they strongly influence whether users return or quietly disappear.
Real-World Relevance of w0wkino Thinking
Although w0wkino may sound conceptual, its impact is deeply practical. Products that embody its principles often feel “obvious” to use, even if they solve complex problems. This is not accidental; it is the result of deliberate alignment between intent and execution.
In real-world applications, thinking can improve onboarding experiences, clarify pricing structures, and simplify decision-making flows. It can transform dense dashboards into meaningful narratives and turn passive users into active contributors.
For tech readers and industry observers, offers a useful lens for evaluating digital products. Instead of asking what a platform does, the more revealing question becomes how it makes people feel while doing it.
The Future Trajectory of w0wkino
Looking ahead, the relevance of is likely to grow rather than fade. As digital products increasingly blend into everyday life, expectations will continue to rise. Users will demand systems that respect their time, attention, and emotional bandwidth.
w0wkino aligns naturally with this future. It does not resist technological advancement; it humanizes it. In doing so, it provides a roadmap for building platforms that remain valuable even as tools and trends change.
For founders planning long-term impact, adopting is less about differentiation and more about durability. Trends come and go, but well-crafted experiences age gracefully.
Conclusion
w0wkino is not a shortcut to success, nor is it a rigid formula. It is a way of thinking that prioritizes harmony between technology and humanity. In a digital world often driven by speed and scale, it offers something rarer: intention.
For entrepreneurs, tech readers, and founders, w0wkino serves as a reminder that the most successful products are not just built—they are felt. When systems make sense, respect users, and tell a coherent story, growth becomes a natural outcome rather than a forced objective.
As digital experiences continue to shape how people work, learn, and connect, the principles behind w0wkino may well define the difference between platforms that are merely used and those that are genuinely valued.
-

 TOPIC8 months ago
TOPIC8 months agoAiyifan: The Digital Platform Transforming Access to Asian Entertainment
-

 blog5 months ago
blog5 months agoFesbuka: How to Maximize Your Experience on the Platform
-

 TOPIC7 months ago
TOPIC7 months agov4holt: Revolutionizing Digital Accessibility
-

 TOPIC9 months ago
TOPIC9 months agoMolex 39850-0500: An In-Depth Overview of a Key Connector Component
-

 blog7 months ago
blog7 months agoBlack Sea Body Oil: A New Standard in Natural Skincare
-

 TOPIC7 months ago
TOPIC7 months agoMamuka Chinnavadu: An Exploration of Its Significance and Cultural Impact
-

 TOPIC9 months ago
TOPIC9 months agoManguonmienphi: Understanding the Concept and Its Impact
-

 TOPIC7 months ago
TOPIC7 months agoGessolini: Minimalist Aesthetic Rooted in Texture
