TECHNOLOGY
How Modern Commercial Security Systems Reduce Business Risks
In an increasingly complex operating environment, businesses face a wide range of risks that extend beyond traditional concerns, such as theft or vandalism. Unauthorized access, internal misconduct, data breaches, and operational disruptions can all threaten continuity and financial stability. Modern commercial security systems have evolved to address these challenges through integrated technologies that emphasize prevention, early detection, and informed response. Rather than functioning as isolated tools, today’s systems combine physical security, digital monitoring, and automated controls to create a more resilient risk management framework.
Advancements such as intelligent surveillance, access control systems, and real-time alerts allow organizations to identify vulnerabilities and respond more effectively to potential threats. These technologies also support better decision-making by generating data that can reveal patterns, inefficiencies, or emerging risks. For businesses seeking to understand how these systems are designed and implemented in real-world settings, general industry resources like signalsolutions.com provide insight into the components and principles behind modern security infrastructure. Overall, commercial security systems play a crucial role in mitigating uncertainty, facilitating compliance, and enabling organizations to maintain safe and reliable operations without relying solely on reactive measures.
AI-Driven Video Surveillance
Surveillance technology has undergone a transformation with the integration of artificial intelligence. Gone are the days of relying solely on human monitoring and analog cameras. AI-driven video surveillance provides real-time analysis, enabling the rapid identification of suspicious activities or policy violations without human oversight. These intelligent systems can detect and classify objects, recognize faces, and alert security teams to anomalies, minimizing incident response times and often preventing crimes before they escalate. AI-powered surveillance is becoming a cornerstone for proactive business risk management.
Cloud-Based Monitoring and Remote Access
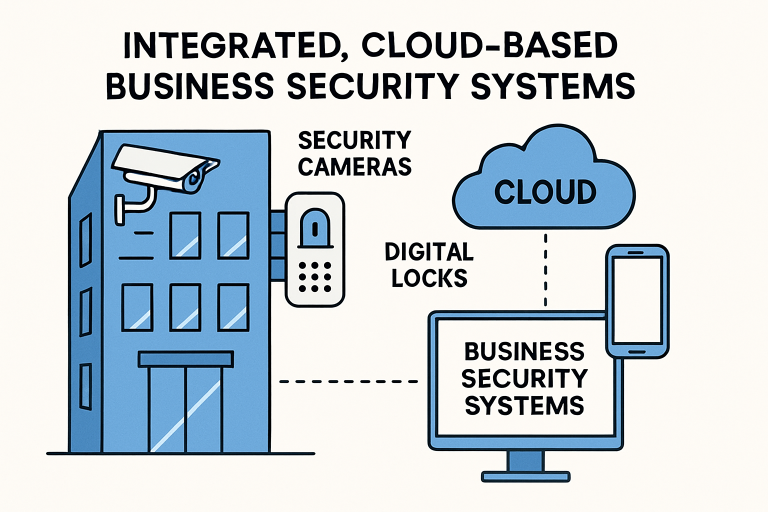
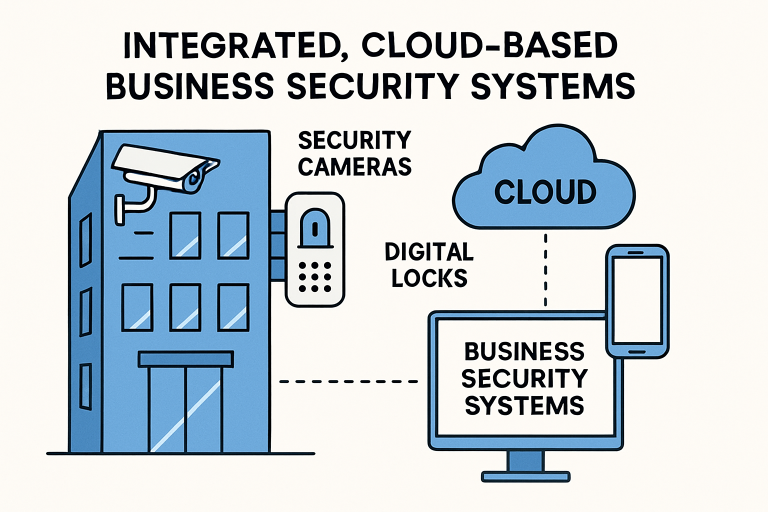
The adoption of cloud-based platforms has redefined how businesses monitor and control their security infrastructure. Cloud solutions allow for the centralized management of multiple locations, providing instantaneous access to live or recorded video feeds, access logs, and security events from any authorized device. This accessibility enables businesses to respond swiftly to emergencies, regardless of the location of their stakeholders.
Moreover, cloud-based systems can be scaled efficiently as a business grows, ensuring that new sites and users can be added with minimal disruption. Automated updates and cybersecurity features also provide protection against emerging digital threats, thereby reinforcing the overall security posture. This real-time, remote functionality proves invaluable for distributed teams and executives on the move.
 Advanced Access Control Systems
Advanced Access Control Systems
Modern access control extends far beyond traditional locks, utilizing technologies such as proximity cards, mobile credentials, and biometric authentication to enhance both security and convenience. These methods help prevent unauthorized entry and tailor access permissions to individual roles and schedules. For instance, cleaning staff may only have access to the building after hours, while IT personnel may have restricted access to server rooms.
Advanced access systems produce detailed audit logs, improving accountability and compliance—key considerations in regulated industries. Notably, smart access control can also integrate with other building systems, such as video surveillance and alarms, offering a unified response to threats and simplifying management for security personnel.
Integration of Physical and Cybersecurity
With the increasing convergence of digital and physical threats, integrating these security domains is vital. A physical breach often leads to cyber vulnerabilities, such as unauthorized access to servers or network devices. Accordingly, a unified approach that includes both on-premises and digital protections is essential for comprehensive risk mitigation.
Forward-thinking businesses develop strategies that monitor both access points and network events, closing potential gaps and strengthening incident response across the board. Industry authorities recommend implementing holistic policies and providing security training to all employees to ensure robust, integrated protection.
Mobile Access Control
Mobile devices are revolutionizing access control, eliminating the need for physical keys and cards. Employees and visitors receive unique digital credentials on their smartphones, which can be updated or revoked instantly if a device is lost or an individual’s role changes. This system significantly reduces the risks and administrative burdens associated with lost or duplicated keys.
Mobile access also enhances user experience, offering convenience and flexibility for businesses with remote work arrangements or multiple branches. With seamless integration into cloud-based monitoring, mobile control further streamlines facility management and emergency response protocols.
Data-Driven Security Planning
Gathering and analyzing security data is critical for identifying trends and making informed decisions about risk mitigation. By integrating data analytics and AI, security teams can predict incident hotspots, optimize resource allocation, and create actionable insights for ongoing protection. For example, analytics solutions can identify which entrances face the most traffic or which times are most prone to security incidents, enabling businesses to focus efforts where they’re needed most.
Data-driven strategies not only enhance prevention but also help justify investments by demonstrating measurable improvements in safety and efficiency. Companies that leverage analytics witness reductions in both security breaches and operational costs, supporting long-term business resilience.
Sustainable Security Solutions
Sustainability is becoming increasingly important in security deployments. Businesses are adopting solar, LED, and low-power technologies to minimize their environmental footprint and reduce costs. Battery-operated, wireless sensors and solar-powered cameras provide reliable performance with minimal energy consumption and no complex wiring, making them ideal for both new builds and retrofits.
By selecting eco-friendly security products and implementing green policies, businesses demonstrate commitment to environmental responsibility while simultaneously lowering utility expenses and maintenance needs. These choices align with broader corporate social responsibility initiatives and appeal to environmentally conscious stakeholders.
Conclusion
Modern commercial security systems are crucial for mitigating business risks and fostering a safe, resilient organizational culture. Embracing AI-driven surveillance, cloud-based management, advanced and mobile access control, and the convergence of physical and cyber protections provides companies with a layered, responsive defense against today’s threats. Combining data-driven planning with sustainable technologies further amplifies the benefits, enabling organizations to operate confidently and responsibly in a dynamic risk landscape. The businesses that keep pace with these security innovations will be best equipped to protect their people, property, and reputation well into the future.
TECHNOLOGY
Xierzugicoz2005– Complete Guide to Meaning, Uses, and Online Relevance
The internet constantly produces new terms, identifiers, and digital codes that spark curiosity among users. One such emerging term is xierzugicoz2005. At first glance, it may appear like a random string of characters, but keywords like this often serve specific purposes in digital systems, usernames, data identification, software environments, or online communities. Understanding such terms helps users navigate the evolving digital landscape more confidently.
The keyword xierzugicoz2005 has begun appearing in search queries, online discussions, and certain digital contexts. While it may not yet be widely recognized, exploring its potential meaning and applications reveals how modern digital identifiers function. In many cases, similar terms are connected to user-generated identifiers, database references, experimental software tags, or creative online identities.
This complete guide explores everything you need to know about xierzugicoz2005. We will examine its possible meaning, structure, uses in digital environments, relevance to modern technology, and why people are searching for it. By the end of this article, you will have a clear understanding of this keyword and its potential role in digital ecosystems.
Understanding the Meaning of Xierzugicoz2005
The keyword xierzugicoz2005 appears to be a compound digital identifier made up of letters and numbers. Such identifiers are common in online environments where unique naming systems are required. These may include usernames, system codes, dataset labels, or experimental identifiers used in software or digital platforms.
In many cases, similar keywords are created to ensure uniqueness within large databases or online communities. Since millions of users and systems operate simultaneously on the internet, platforms often rely on distinctive combinations of characters to avoid duplication. A term like xierzugicoz2005 could represent a unique digital identity or reference point within a particular system.
Another aspect to consider is that the number portion, 2005, may indicate a year, version number, or system release marker. Many digital naming conventions include numbers to signify timelines, versions, or generational updates. Understanding this structure helps interpret how such identifiers are created and why they appear in search results.
Structure and Composition of Xierzugicoz2005
The structure of xierzugicoz2005 reveals several clues about how the term may have been formed. The first portion consists of alphabetic characters, while the second portion contains a numerical sequence. This combination is widely used in digital identifiers because it increases the number of possible unique variations.
Alphabetic characters often serve as the primary identity portion of a keyword. They may represent an invented term, abbreviation, or creative name chosen by a developer or user. In the case of xierzugicoz, the word appears to be a synthetic or generated string rather than a traditional dictionary term.
The numeric element 2005 can serve several possible roles. It might represent a year associated with a project, a version number, or simply an additional element used to ensure the name remains unique within a system. Many digital platforms automatically append numbers to usernames or identifiers when the original name is already in use.
Example Structure Breakdown
| Component | Possible Meaning |
|---|---|
| Xierzugicoz | Unique identifier or generated keyword |
| 2005 | Year reference, version number, or unique suffix |
| Combined Term | Distinct digital identifier |
This structure demonstrates how simple combinations of letters and numbers can create thousands of unique identifiers for digital systems.
Possible Origins of Xierzugicoz2005
The origin of xierzugicoz2005 is not clearly documented, but it likely emerged from a digital environment where unique identifiers are necessary. Such environments include gaming platforms, coding repositories, experimental software projects, or user-generated accounts.
One possibility is that the keyword originated as a username or account identifier. Online communities often encourage creative usernames, and users frequently combine invented words with numbers to create something unique and memorable.
Another possibility is that xierzugicoz2005 was generated automatically by a system. Some software platforms create random strings to label temporary files, datasets, or internal system elements. These generated identifiers help prevent conflicts when multiple processes operate simultaneously.
Why People Are Searching for Xierzugicoz2005
Search interest in xierzugicoz2005 may be driven by curiosity or by users encountering the term in digital environments. When people see unfamiliar identifiers in software interfaces, system logs, or online platforms, they often search for more information to understand what the term represents.
Another reason could be its appearance in specific online communities or forums. Once a keyword begins circulating online, even a small number of mentions can lead to increased search activity. This often happens with experimental software tags or unique digital identities.
In some cases, search interest may also arise from technical troubleshooting. If a system error, file name, or dataset label includes xierzugicoz2005, users might search for it while trying to resolve a problem or understand the context.
Digital Identifiers and Their Importance
Digital identifiers like xierzugicoz2005 play a crucial role in modern computing systems. These identifiers help systems organize data, distinguish users, and track processes across complex digital infrastructures.
Without unique identifiers, databases would struggle to manage large volumes of information efficiently. Each file, account, or system component needs a unique label to prevent conflicts and ensure accurate processing.
For example, when a new user creates an account on an online platform, the system must verify that the username is unique. If the chosen name already exists, the platform often suggests variations that include numbers or additional characters.
Common Uses of Digital Identifiers
- Usernames and online profiles
- Software version labels
- Database records
- Temporary system files
- Gaming accounts
These examples demonstrate how identifiers like xierzugicoz2005 may appear in many different contexts.
Role of Xierzugicoz2005 in Online Systems
If xierzugicoz2005 is being used within a digital system, it may function as a unique reference point. Systems rely heavily on such references to track activities, store data, and manage operations efficiently.
For instance, software applications often assign unique identifiers to files or transactions. These identifiers ensure that each action within the system can be tracked without confusion.
Similarly, online platforms frequently assign random identifiers to users, posts, or internal database entries. This allows systems to handle millions of records while maintaining clear organization.
Xierzugicoz2005 and Online Usernames
One of the most common uses for unique identifiers like xierzugicoz2005 is in usernames. Because many platforms already have millions of registered accounts, users often need to create distinctive names that include both letters and numbers.
A username such as xierzugicoz2005 would likely be unique enough to avoid duplication. This makes it suitable for platforms such as forums, gaming networks, or social media services.
Creative usernames often combine invented words with numbers that have personal meaning, such as a birth year or favorite number. This pattern closely matches the structure seen in the keyword being analyzed.
Possible Technical Contexts for Xierzugicoz2005
There are several technical environments where a term like xierzugicoz2005 might appear. These environments rely on unique identifiers to manage processes, files, or system components.
Technical Environments
| Environment | Possible Role |
|---|---|
| Software Development | Internal file or module identifier |
| Databases | Record or dataset label |
| Gaming Platforms | Player account name |
| Cloud Systems | Temporary resource identifier |
Each of these contexts requires unique identifiers to ensure that operations remain organized and efficient.
How Digital Naming Conventions Work
Digital naming conventions help maintain order in systems where millions of identifiers must coexist. These conventions often combine letters, numbers, and sometimes symbols to create unique names.
The alphabetic portion of a name typically serves as the recognizable component. The numeric portion helps ensure uniqueness, especially when similar names already exist.
Systems may also apply specific rules for generating identifiers automatically. These rules help maintain consistency while preventing conflicts within databases or platforms.
Security Considerations for Unique Identifiers
Identifiers like xierzugicoz2005 can sometimes be linked to accounts or digital assets. Because of this, security practices are important when creating or managing such identifiers.
Users should avoid sharing sensitive account identifiers publicly if they are associated with login credentials or private systems. Even though an identifier itself may not grant access, it can sometimes reveal information about internal structures.
Organizations also implement safeguards to prevent unauthorized access to systems that rely on unique identifiers. These safeguards include authentication protocols, encryption, and monitoring systems.
How Keywords Like Xierzugicoz2005 Spread Online
The internet allows even obscure keywords to spread rapidly. A single mention in a forum, blog post, or technical documentation can lead to increased search activity.
Search engines also contribute to this process by indexing pages that contain the keyword. Once indexed, the keyword becomes searchable, allowing more users to discover it.
In some cases, online communities adopt unusual terms as part of inside jokes or shared references. This cultural phenomenon can cause previously unknown identifiers to gain sudden popularity.
Potential Future Relevance of Xierzugicoz2005
Although xierzugicoz2005 may currently appear as an isolated keyword, its relevance could grow if it becomes associated with a specific project, platform, or digital identity.
Technology evolves rapidly, and many widely recognized terms started as obscure identifiers. If the keyword becomes linked to a popular application or community, it could eventually gain broader recognition.
For now, it serves as an example of how digital naming systems work and why unique identifiers are essential in modern computing.
Conclusion
The keyword xierzugicoz2005 illustrates how digital identifiers function in modern online environments. Whether used as a username, system code, or database reference, such terms play a vital role in organizing and managing digital information.
By examining its structure, possible origins, and potential uses, we gain insight into the broader systems that power the internet. Unique identifiers ensure that millions of users, files, and processes can coexist without confusion.
As technology continues to evolve, identifiers like xierzugicoz2005 will remain an essential component of digital infrastructure. Understanding their purpose helps users navigate online systems more effectively and appreciate the complexity of the digital world.
FAQ’s
What is xierzugicoz2005?
Xierzugicoz2005 appears to be a unique digital identifier made up of letters and numbers. It may function as a username, system code, or database label.
Why are people searching for xierzugicoz2005?
People may search for it after encountering the term in online platforms, system logs, or digital discussions.
Is xierzugicoz2005 a person or brand?
Currently, there is no confirmed evidence that it represents a person or established brand.
Where might xierzugicoz2005 be used?
It could appear in online accounts, gaming platforms, software systems, or database records.
Are unique identifiers like xierzugicoz2005 important?
Yes, they help digital systems organize data, manage users, and track processes efficiently.
TECHNOLOGY
DashGameFest: A Comprehensive Guide to the Ultimate Gaming Festival

In the ever-evolving world of video games, festivals celebrating gaming culture have become significant events for both gamers and developers alike. One such festival that has gained remarkable popularity is DashGameFest. In this article, we will dive deep into DashGameFest, exploring its origins, what attendees can expect, and the impact it has on the gaming community.
What is DashGameFest?
DashGameFest is a gaming festival that brings together gamers, developers, industry experts, and enthusiasts under one roof. This exciting event celebrates video games in all their forms—console, PC, mobile, and even tabletop gaming. DashGameFest acts as a platform for both new and established creators to showcase their latest titles, and it offers a space for networking, learning, and community building.
The Origins of DashGameFest
DashGameFest emerged in response to the need for a more community-oriented gaming event that emphasizes inclusivity and creativity. With gaming’s rapid growth in recent years, a festival was necessary to honor the diverse nature of the industry. The inaugural event took place in [Year], and since then, it has grown exponentially—drawing thousands of attendees from various backgrounds, ages, and gaming preferences.
The Founders’ Vision
The founders of DashGameFest aimed to create an environment where players could connect with developers, participate in engaging activities, and discover new games that reflect their interests. They sought to inspire collaborations between creators and gamers, leading to innovative projects that enrich the gaming landscape.
What to Expect at DashGameFest
Showcases and Exhibitions
One of the main highlights of DashGameFest is the array of showcases and exhibitions where developers display their upcoming projects. Attendees get an exclusive first look at fresh releases and exciting indie games that may not be found in mainstream media. Game developers are on hand to demonstrate their titles, explain their design choices, and even gather feedback from players.
Panels and Workshops
DashGameFest provides a stimulating environment for learning through various panels and workshops. Industry experts discuss trending topics, providing insights on game design, storytelling, monetization strategies, and future technology in gaming. These sessions not only educate but also inspire participants to explore new ideas and approaches.
Competitive Gaming and Tournaments
For those who thrive on competition, DashGameFest hosts a series of gaming tournaments across popular titles. Gamers of all skill levels can participate, offering both casual and hardcore players a chance to test their abilities and win impressive prizes. These tournaments foster friendly rivalry and encourage community companionship, solidifying the event’s status as a gathering of gaming enthusiasts.
Networking Opportunities
Networking is a crucial aspect of DashGameFest. Gamers, developers, and industry professionals come together to share ideas, collaborate, and forge potential partnerships. Whether through informal mixers or structured meet-and-greets, attendees can expand their social circles and enhance their understanding of the gaming industry.
Community Engagement
At its core, DashGameFest is dedicated to building a sense of community among gamers. The event features sessions and activities aimed at fostering inclusivity, diversity, and support for marginalized voices in gaming. From spotlighting women developers to promoting environmental sustainability within game design, DashGameFest emphasizes social responsibility.
The Impact of DashGameFest on the Gaming Community
The presence of specialized gaming festivals like DashGameFest has had a profound impact on the gaming community. Here’s how:
Supporting Indie Developers
By providing a platform for indie developers, DashGameFest enables smaller creators to gain visibility in a crowded industry. Attendees can discover innovative games and support creators financially, encouraging more diversity in the types of games produced.
Building Community Bonds
DashGameFest fosters a sense of belonging among gamers by creating safe spaces for people to gather and share their experiences. These relationships often extend beyond the festival, giving rise to gaming groups, online communities, and even friendships that span across geographical boundaries.
Encouraging Innovation
As developers share their ideas and receive feedback from users, they are motivated to experiment and innovate, pushing the boundaries of game design. The collaborative spirit of DashGameFest ignites the creative process, leading to unique gaming experiences that may otherwise never come to fruition.
Raising Awareness for Social Issues
The festival’s focus on diversity, inclusion, and social responsibility encourages conversations about important issues within the gaming industry. These discussions can lead to crucial changes, both in terms of representation in games and in how gaming companies conduct their business.
Final Thoughts
DashGameFest represents the dynamic and vibrant nature of the gaming industry. As a festival that celebrates creativity, community, and connection, it offers something for everyone involved in the gaming ecosystem.
Whether you are a passionate gamer, an eager developer, or someone interested in learning more about the industry, DashGameFest provides a unique opportunity to be part of the evolving narrative of gaming culture. As the festival continues to grow and attract more attendees and developers, it is poised to become a cornerstone event in the annual gaming calendar, leaving a lasting legacy in the hearts of gamers everywhere.
TECHNOLOGY
5618237277: Understanding the Significance and Implications of This Number

In an increasingly connected world, phone numbers not only serve as a means of communication but also hold various implications regarding identity, privacy, and service access. One such number, 5618237277, has gained attention, igniting curiosity about its origin, purpose, and any significance it may possess. In this article, we will delve into the various aspects surrounding the number 5618237277, from its potential uses to implications on privacy and communication.
Understanding Phone Numbers
Before we dive deeper into the specifics of 5618237277, it’s essential to understand how phone numbers work. In most countries, phone numbers are designed to be unique identifiers for individual telephones or mobile devices. They consist of various components, such as country codes, area codes, and the subscriber number, which together create a format that allows for effective routing of calls.
Anatomy of a Phone Number
Using the example of 5618237277, we can break down the structure into its components:
- Country Code: Indicates the country from which the call is made. In the case of the United States, which the area code of 561 suggests, the country code is +1.
- Area Code: The digits at the start of this number (561) indicate the geographical area of the phone line. In the US, area codes often correspond to specific regions or cities.
- Subscriber Number: The remaining digits (8237277) differentiate between differentphone subscribers in that area code.
What is 5618237277?
Now, let’s focus specifically on the number 5618237277. This 10-digit phone number is likely associated with a location based in or near the Palm Beach County area, as the area code 561 encompasses several cities within South Florida, including West Palm Beach, Boca Raton, and Delray Beach.
Possible Uses of the Number
- Personal Use: The number could belong to an individual, making it part of their personal life or professional endeavors. Receiving calls or texts from 5618237277 may therefore relate to direct communication with a friend, family member, or colleague.
- Business Contact: Alternatively, this phone number could belong to a local business or service provider. Many businesses utilize specific numbers to establish a clear point of contact with customers.
- Telemarketing and Custom Services: In today’s economy, telemarketing remains prevalent. The number could be associated with marketing campaigns, automated services, or other commercial uses. Often, businesses leverage numbers with specific area codes to give the impression of local services.
- Scams and Spam: Unfortunately, in an age of growing concern over privacy, numbers like 5618237277 can sometimes be linked to unwanted calls, scams, or spam. It is crucial to remain aware of such possibilities, including verifying the intent of the caller before sharing personal information.
The Impact of Caller ID and Traceability
One valuable aspect of modern phone communication is the availability of Caller ID. This service enables recipients to see the number of an incoming call before answering. The significance of this information is vast:
- Identification: When receiving a call from 5618237277, the recipient can decide whether to answer based on familiarity or willingness to engage.
- Spam or Scam Detection: Many services identify known spam numbers, keeping individuals informed and protecting them against potential fraud.
- Traceability: In the case of harassment or repeated unwanted calls, the ability to track the origin number allows individuals to report instances to authorities.
Privacy Considerations
With the ease of finding and sharing phone numbers comes the challenge of privacy. The number 5618237277, like any other phone number, can raise privacy concerns:
Personal Data Security
Understanding how your personal information is tied to your phone number is vital. Unmonitored sharing of phone numbers can lead to issues such as identity theft. If your number becomes publicly available, it can be utilized in malicious ways.
Opting Out
If you frequently receive unwanted calls from numbers like 5618237277, you may consider registering your number with the National Do Not Call Registry, which can help mitigate unsolicited contacts.
Reporting Suspected Scams
If you suspect that the caller from 5618237277 is attempting a scam, it is crucial to report it to the appropriate authorities. Websites like the Federal Trade Commission (FTC) and local consumer protection offices provide tools and channels for reporting fraudulent activity.
Conclusion
The number 5618237277 serves as a reminder of the complexities inherent in modern phone communications. As a representative of a potential personal, business, or even malicious connection, it encapsulates the intricate interplay of identity, privacy, and security in our digital age. Understanding the significance of such numbers empowers individuals to navigate their communications more effectively, ensuring safety and clarity in their interactions.
-

 TOPIC5 months ago
TOPIC5 months agov4holt: Revolutionizing Digital Accessibility
-

 TOPIC8 months ago
TOPIC8 months agoMolex 39850-0500: An In-Depth Overview of a Key Connector Component
-

 blog6 months ago
blog6 months agoBlack Sea Body Oil: A New Standard in Natural Skincare
-

 TOPIC5 months ago
TOPIC5 months agoMamuka Chinnavadu: An Exploration of Its Significance and Cultural Impact
-

 TOPIC6 months ago
TOPIC6 months agoGessolini: Minimalist Aesthetic Rooted in Texture
-

 TOPIC7 months ago
TOPIC7 months agoManguonmienphi: Understanding the Concept and Its Impact
-

 TOPIC8 months ago
TOPIC8 months agoDorothy Miles: Deaf Poet Who Shaped Sign Language
-

 TOPIC7 months ago
TOPIC7 months agoAiyifan: The Digital Platform Transforming Access to Asian Entertainment
